
The companies you trust rely on Thales
Get a Free Maxtec CyberSecurity HealthCheck

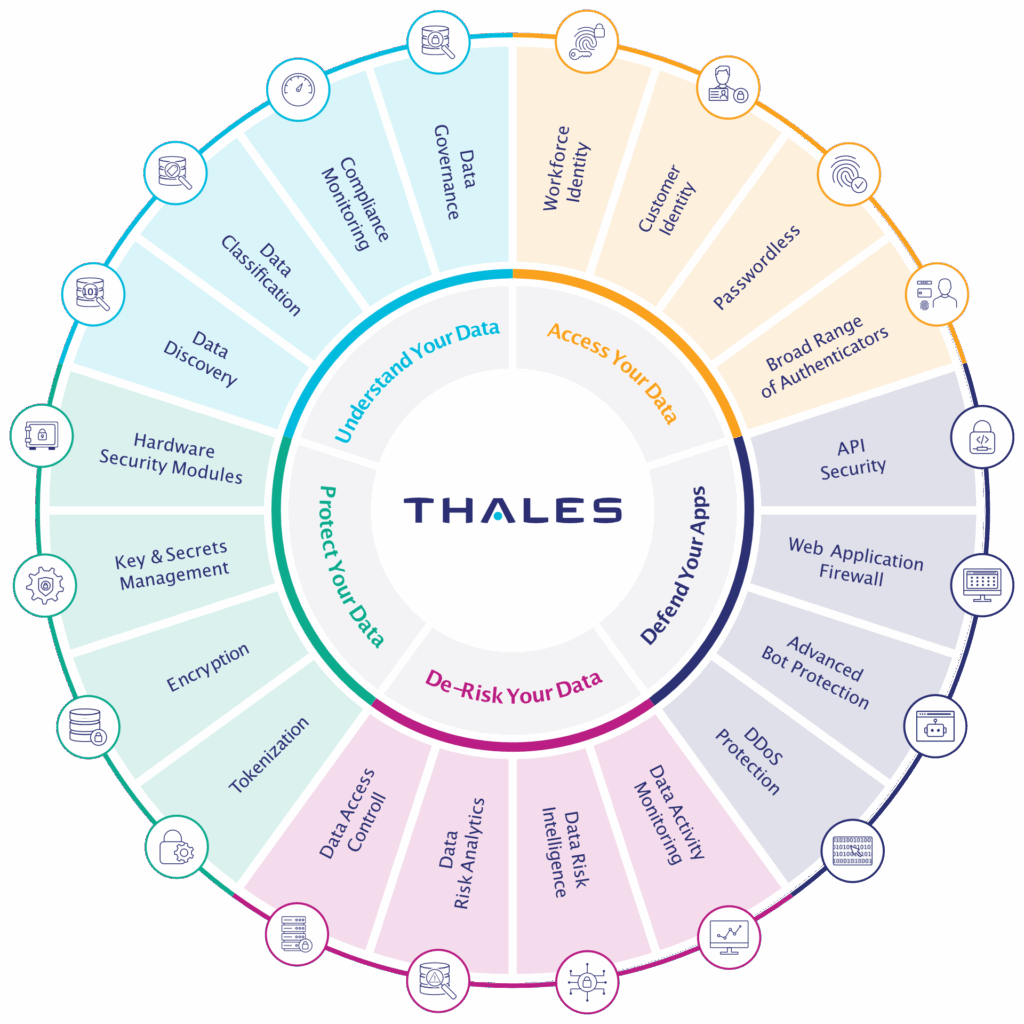
Security for a World Powered by Applications, Data, Identities, and Software
Through innovative and integrated platforms, Thales helps organisations operate securely in the cloud, defend against cyber threats, accelerate compliance, and deliver trusted digital experiences for billions of consumers every day.
KEY BENEFITS

Data Discovery and Governance
Understand where sensitive data lives and how it is used with deep discovery, classification, and governance capabilities.

Data Protection and Control
Protect data across environments using strong encryption, tokenisation, and key management.

3 second DDoS SLA
Guaranteed 3-second mitigation SLA for Layers 3 and 4 DDoS attacks.

Application Security
Safeguard web applications and APIs against attacks with firewalls, bot protection, and DDoS mitigation.

Data Risk Intelligence and Monitoring
Continuously monitor data activity, detect anomalies, and identify insider risks with behavioural analytics.

Compliance and Audit Readiness
Meet regulatory requirements with built-in auditing, data residency controls, and compliance visibility.

Flexible, Cloud-Ready Architecture
Enable hybrid and multi-cloud security with interoperable modules that scale with your environment.
APPLICATION SECURITY
DATA SECURITY
APPLICATION SECURITY
DATA SECURITY
Data Activity Monitoring
Data Risk Analytics
Data Retention & Archive
Data Discovery and Classification
Data Encryption
Key Management
Secrets Management
Data Protection on Demand
General Purpose Hardware Security Modules
Payment Hardware Security Modules
Network Encryptors
Secure File Sharing
Data Risk Prioritization
Static Data Masking

Protect Your Critical Assets with Imperva
Request a Free Trial
to see how Imperva can secure your data and applications against the latest threats.
Application Security
Applications help to drive digital transformation, but traditional security approaches can’t keep pace with dynamic, multi-cloud, and hybrid environments, which leave you exposed to zero-day threats.
Overview
Thales Web Application Firewall (WAF) automatically stops advanced attacks on hybrid and cloud-native environments enabling organizations to protect applications anywhere.

Overview
Thales Advanced Bot Protection prevents sophisticated automated attacks against your most valuable business applications without sacrificing business-critical traffic.

Overview
Thales Client-Side Protection identifies risky JavaScript code and detects attempts to exploit it to prevent supply chain fraud from client-side attacks like formjacking, digital skimming, and Magecart.

Overview
Thales Runtime Protection applies a positive security model to application runtime environments to protect your applications against software supply chain and zero-day attacks from the inside out.

Overview
Thales DDoS Protection secures the entire application layer against potential disruptions, so you can focus on continuous availability to your customers.

Overview
Thales API Security provides deep discovery of all APIs and sensitive data to enable security teams to establish a positive security model. Finally, security can keep pace with the rapid changes from DevOps.

The Thales data Security Fabric difference

Provides broadest coverage across multicloud, hybrid, and on-premises environments
Broadest coverage ensures your entire data estate is secure
Robust and consistent security policy application across multicloud, hybrid cloud, and on-premises data store topologies

Protects any data sources and types, across structured, semi-structured, & unstructured
Any data, everywhere: from structured to semi-structured to unstructured
Imperva DSF provides a comprehensive and unified view of enterprise data risks across both structured and unstructured data management systems – meaning your security policies are applied consistently everywhere.
DSF can standardize data security controls across large and complex data environments so you have full visibility and centralized command of what is happening across all of your file stores and data assets, on-premises, in the hybrid cloud, and across multiple clouds.

Integrates with ecosystem technologies for incident context and additional data capabilities
Integrates with your existing ecosystem technology investments
For both incident context and additional data capabilities — fully leveraging DSF automated workflows.
Imperva Data Security Fabrice integrates with your existing security and information technology ecosystem, combining technologies for the highest resolution of data risk exposure.
With thousands of playbooks, security actions can be orchestrated and automated — accelerating decision processes and incident investigations.

Unifies visibility, control, automation & insights via a single data service or dashboard
Unifies visibility, control, workflow automation, and insights via a single dashboard
Protect data by understanding and controlling access by users, processes, and apps within a single service view.
Imperva Data Security Fabrice provides full enterprise visibility of multicloud and hybrid threats, risk, and activity across the entire data estate.
Protect any data source by understanding and controlling access by users, processes, and apps within a single service view — while machine learning algorithms detect and alert you to anomalous and bad behavior.

Backup and Recovery

Integrated. Automated.Cybersecurity

Qualys Trurisk Platform

Application & Data Security

Industry-Leading Cloud Security

Agentless Data Loss Prevention

Cloud-Native Saas Deployment

Certificate Management

Secure Storage

Delivers all-in-one IT management

Is a powerful collaboration and PDF workflow solution

Secure Remote Support

Application & Data Security
Unified Endpoint Management






